For decades, Macro viruses are a serious problem. Does it mean that Windows, Office and VBA – all Microsoft products – are insecure?
Absolutely not. Microsoft gave you the ability to stop Macro viruses
– instantly – ever since Office existed (25 years+).
This is a technical article – for Security and IT professionals.
Reading time (7 min)
Contents
Stop Macro viruses – exactly how?
Macro means some code written in VBA – Visual Basic for Applications. There are three types of macros – from a security point of view.
Type 1:
Macros containing malicious or dangerous code – viruses (malware).
Type 2:
Macros created / written by users to do some useful things.
We want to block Type 1 only.
Type 2 are useful and should not be blocked.
Change this setting to stop Macro viruses
- You can change the setting for each Office product separately
- Most users create macros in Excel. So it is safe to disable macros totally for other applications like Word, Outlook, PowerPoint, Visio and Project. (OneNote does not support macros.)
- The setting is available in File – Options – Trust Centre – Trust Centre Settings – Macro Settings
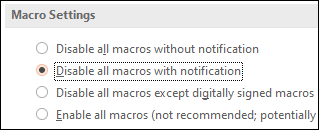
- The default is Disable all Macros with Notification
- This basically means, any macro will not run by default.
- Unfortunately, it is not safe in practice – because it shows a Notification to users – the Enable Macros dialog.
- This means – business users – with know knowledge about cybersecurity or programming have to decide whether to Enable the macro or not. This is where the problem lies.
- Most users say Yes and that is how the malicious code (virus) runs.
Stop running macros
The safest option is to Disable all macros without Notification. Apply this to applications where users have not created their own macros. This is the safest option. With this option activated, macro viruses will simply not run – even if you do not have any other anti-virus or other protection running.
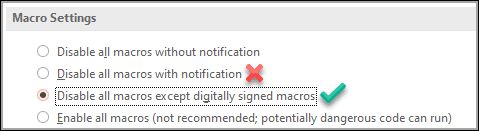
Stop running bad macros only
This is done using the option
Disable all macros except digitally signed macros
Ideally, your organization should purchase an Authenticode Certificate from a certifying authority and sign all useful macros created by business users. These macros will run without a problem. But viruses will not run.
Why wont a macro virus be digitally signed?
Well, viruses are written by bad people. They are committing a crime. Obviously, they do not want their identity to be known – else they will be caught and prosecuted immediately.
Digital Signature cannot be purchased just like that. You need to submit your identity details (corporate identity – in case of Authenticode Certificate) and it is verified by the certifying authority.
That is why, no hacker is going to get a digital signature.
Let users sign their own macros
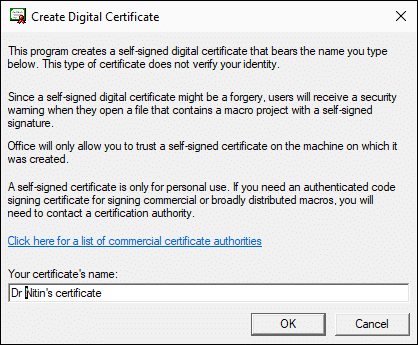
Another option is to create a certificate at individual user level. In Office folder (all versions of Office) there is a file called SELFCERT.EXE
This file can be used by any user to create a local Digital Certificate.
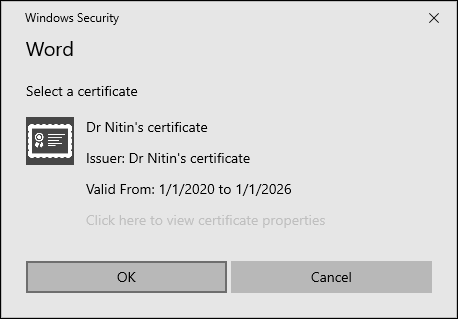
This certificate can be used to Digitally Sign macros created by the same user. This certificate works only on the machine where it was created.
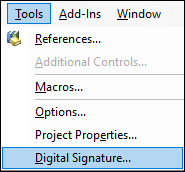
To sign a macro project, open the VBA editor
Go to Tools – Digital Signature…
Choose the Digital Signature created using SELFCERT.EXE and save the project.
Now this macro will run without a problem. But macro viruses will not run.
Warning: Beware of internal hacking
Although the SELFCERT.EXE approach works, remember that 50% of hacking or security compromises happen internally. Therefore, every macro written by a user is a potential security risk – unless proved otherwise.
Therefore, for ensuring protection against internal threats, it is highly recommended that you have an internal team which evaluates user driven macro code from a security point of view. Only macros which are approved by this team should be signed by the organizational Authenticode Digital Certificate and allowed to run.
I do agree that this is extra effort, especially if you have many user created macros. But that is life!
You can purchase Organizational Authenticode Certificates from
various Certifying Authorities.
There are many types of Digital Certificates. It is best to discuss with the desired CA pre-sales support team to ensure you purchase the correct type of certificate.
How to stop Macro viruses across the organization
What we discussed above was at an individual user level. Next step is implement these steps across the organization – in an automated manner.
- This is easily done using AD and Group Policy or Azure AD and Intune (Endpoint manager).
- Extensive settings are available for controlling macro behaviour by individual application
- You can also refine the settings for specific group of users by using AD security groups.
Additionally, you can enable Attack Surface Reduction to protect against malicious behavior arising from macro code.
This is relevant only when macros are allowed to run.
Better still use Safe Attachments
Microsoft has gone one step further and provided another level of security – in case all else fails. For whatever reason, suppose a user opens an infected attachment and the malicious code is running… This is a new malicious code and no antivirus has a solution for it – this is called a Zero Day attack.
Now what protection do we have?
That is where Safe Attachments comes in. All attachments which do not seem to contain malicious code are redirected to a safe place somewhere in the cloud. The file is run there to check what the code does. If it misbehaves, the file is simply blocked. If the file is safe, then it is available to users. It is like a bomb being detonated in a remote, safe area under supervision by experts.
This is called Office 365 Advanced Threat Protection Safe Attachments
Further reading
Here are details of code signing for VBA Projects to stop macro viruses.
Here is a detailed discussion by UK Government (NCSC) about Macro security settings for Office (updated on Oct 2019 at the time of writing this article).
Hope you found this article useful and relevant.
Go ahead and stop macro viruses NOW!


3 Responses
Thanks. This is really helpful. On the one drive app for iOS, can you multi select files to share?
On iOS and Android it is possible to multi-select files and share. It will download and ZIP the files before sharing.
Yes Mult-select and share is available on Android and iOS apps. It will first download the files – zip them and then share the zip.
If you multi-select and share files, it will NOT create a separate link for files. That will be confusing and unmanageable. Hence the zip approach.
On the other hand, a single link cannot be created for multiple files – security will go for a toss.
So what you really want is to first put the files in a folder and then share the folder.